Powerful Features to Simplify and Automate Your Contracts
Legal Templates
Access a library of lawyer-reviewed templates for essential business documents like shareholder agreements, NDAs, and sales contracts. Customisable and compliant, they’re ready for you to use in minutes.
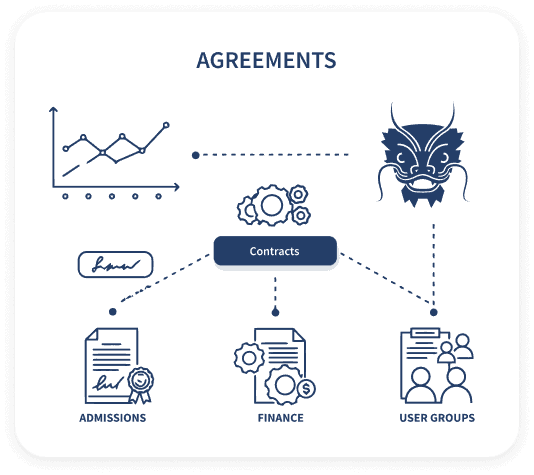
Contract Management (CLM)
Manage the full contract lifecycle from one platform. Create, send, sign, store, and track contracts easily, with automated reminders, renewal alerts, and version control. Full visibility with zero hassle
AI Document Builder
Let AI create contracts for you with just a few simple inputs. Our smart builder drafts legally sound documents, reducing human error while speeding up the process. Perfect for teams needing both speed and quality.
ZegalSign (E-signature)
Secure, legally binding e-signatures from anywhere. No logins or downloads needed, with detailed audit trails for compliance. Fast, easy, and fully compliant.
Real-Time Insights
Track every contract in real-time with dashboards showing who’s signed, who’s pending, and where bottlenecks are. Export reports for deeper analysis and better decision-making.
Integration Hub
Seamlessly connect Zegal with your existing tools — CRMs, HR platforms, cloud storage, and more. Sync data automatically to eliminate manual entry, and set up in no time with flexible API and integrations.
Industries
Education
Automate admissions and HR workflows to reduce admin time and improve compliance across schools and universities.
Real Estate
Digitise leasing contracts and approvals — faster, cleaner, and always audit-ready.
Startups
Get your legal docs sorted fast — from NDAs to shareholder agreements — so you can focus on growth.
Use Cases
Human Resources(HR)
Simplify hiring with automated contracts, faster approvals, and centralised records.
Admissions
Generate, send, and track student contracts in seconds — fully digital and SIS-ready.